Insights, Page 1
How to Better Use Microsoft Copilot to Work Smarter
September 23, 2025
Microsoft Copilot is changing the way businesses work by integrating artificial intelligence directly into the Microsoft 365 apps we use every day. Whether you’re writing an email, analyzing data, or preparing for… Read more
Leadership should see IT as an investment, not a cost center
September 16, 2025
Leadership should see IT as an investment, not a cost center. For example, a server replacement might cost $10–11K upfront, but what’s the cost of your business being completely down for two… Read more
Webinar: 5 Critical Tech Actions for Non-Technical Business Leaders
July 15, 2025
Join us for an interactive webinar designed for business owners, CEOs, CFOs, and operational leaders looking to prevent interruptions, strengthen security, and boost team performance. Too often, technology decisions are left entirely to internal IT teams… Read more
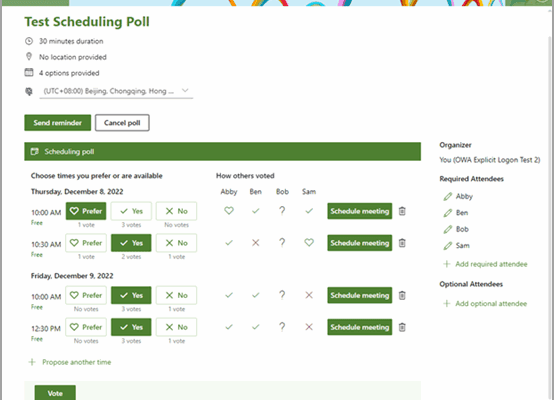
Still Sending Endless Emails to Schedule a Meeting?
June 25, 2025
If scheduling a meeting feels like a never-ending email thread or a 15-minute search through calendars, there’s a better way. Instead of relying on the phrase, “Just let me know what works… Read more
Maximize your Microsoft 365 investment
May 28, 2025
If you’re only using Microsoft 365 for email and excel documents, you’re likely overlooking tools you already have and might even be paying extra for elsewhere. Tools like OneDrive, Microsoft Teams, and… Read more
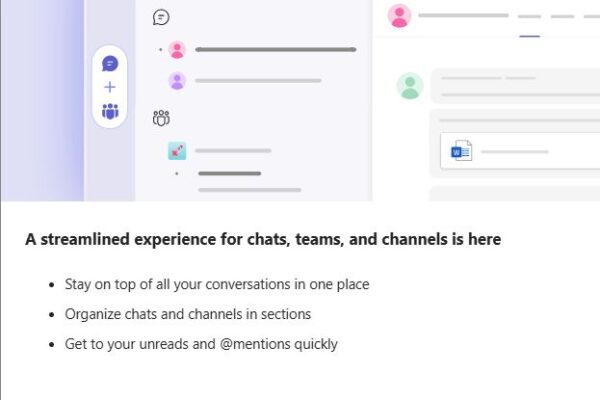
Microsoft Teams streamlined experience for navigating chats, teams, and channels
April 23, 2025
Microsoft Teams Just Got an Upgrade: Here’s What Leaders Need to Know A new feature update quietly rolled out in Microsoft Teams and it could be a welcome change for busy teams… Read more
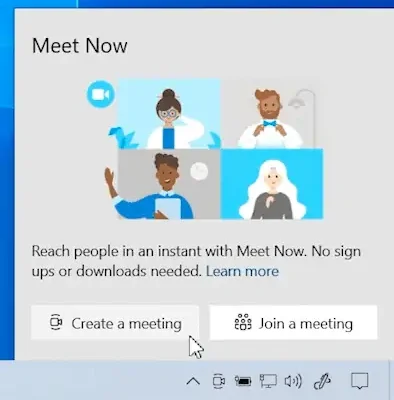
Try the Meet Now feature in Microsoft Teams!
April 16, 2025
Looking to connect on a video call instantly with your team? Try the Meet Now feature in Microsoft Teams! Whether it is a quick catch up, brainstorming session, or impromptu virtual meeting,… Read more
Is your business truly protected 24/7?
March 24, 2025
Is your business truly protected 24/7? A SIEM (Security Information and Event Management) solution is more than just a compliance tool—it’s a crucial asset for business security. ✅ Detect threats early, whether… Read more
Buying business grade devices from a certified partner reseller vs Amazon
March 11, 2025
Why buying business-grade devices from a certified partner reseller vs. Amazon is the best choice. Saving on Amazon might seem like a good idea but you run the risk of ending up… Read more